Jack B. Reid
jack@jackbreid.com
Github profile: jackreid Hosted on GitHub Pages — Theme by mattgraham
Assessing And Mitigating Vulnerability Chains In Model-Centric Acquisition Programs
Spring 2017 - Spring 2018
During my masters program at MIT, I worked under Dr. Donna Rhodes at the Systems Engineering Advancement Researched Initiative (SEARri). This group, as the name suggests, focused on systems engineering, with particular focus on the defense, aerospace, and marine industries. My thesis work focused on assessing vulnerabilities in model-centric acquisition programs. An associated conference presentation is available here and the thesis itself is available on MIT’s DSpace archive.
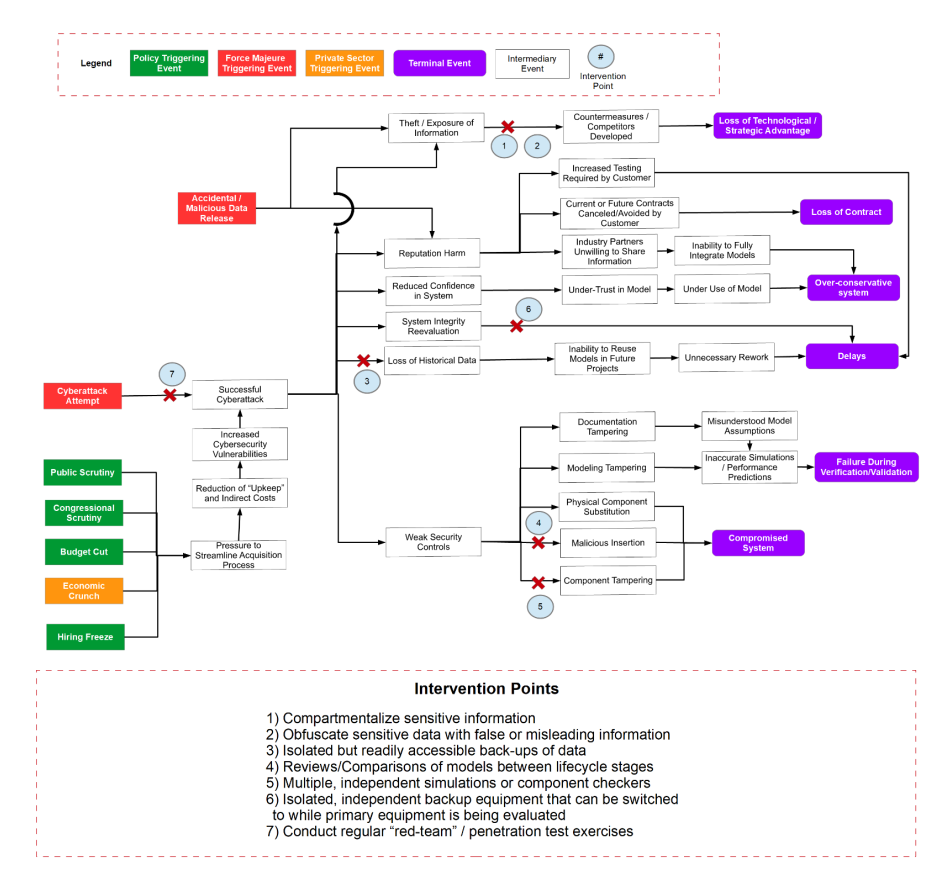
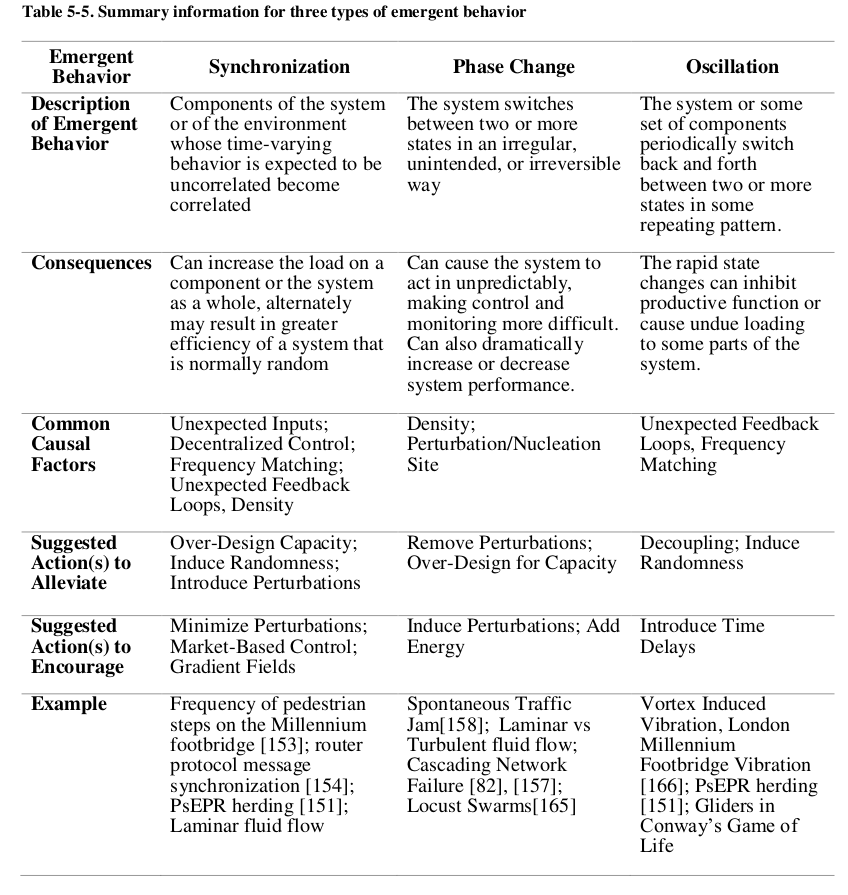
Acquisition programs increasingly use model-centric approaches, generating and using digital assets throughout the lifecycle. Model-centric practices have matured, yet in spite of sound practices there are uncertainties that may impact programs over time. The emergent uncertainties (policy change, budget cuts, disruptive technologies, threats, changing demographics, etc.) and related programmatic decisions (e.g., staff cuts, reduced training hours) may lead to cascading vulnerabilities within model-centric acquisition programs, potentially jeopardizing program success. Program managers are increasingly faced with novel vulnerabilities. They need to be equipped with the means to identify model-centric program vulnerabilities and determine where interventions can most effectively be taken. In this research, Cause-Effect Mapping (CEM), a vulnerability assessment technique, is employed to examine these vulnerabilities. Using a combination of literature investigation, expert interviews, and usability testing, a CEM is created to represent the novel vulnerabilities posed by model-centric practices in acquisition programs. Particular attention is paid to cybersecurity vulnerabilities, which pose a serious threat to the successful implementation of model-centric practices. From this CEM, key gaps in program manager knowledge and organizational policies are identified and potential responses proposed.